Can you account for everyone and everything that has remote access to your corporate network?
In the age of the gig economy, companies have to adapt a more distributed workforce in order to stay competitive and continue to grow. Therefore remote access to enterprise resources is an important requirement for the distributed and outsourced nature of modern work.
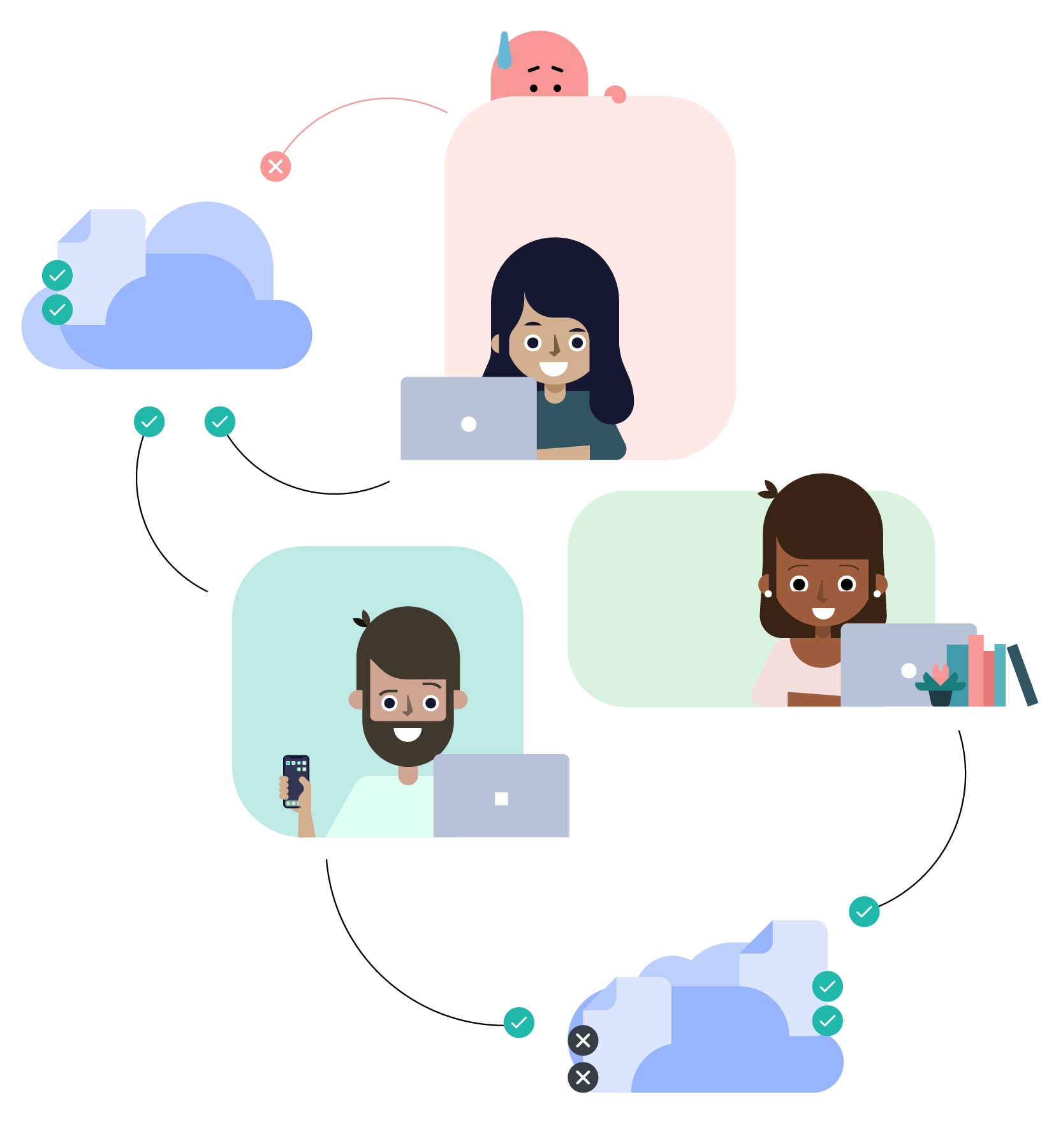
Traditionally, enabling remote access to an internal network or private cloud has been a high risk decision. The typical problems are password or access key re-use and sharing by contractors, poor or no internal network segmentation, limited visibility into what resources get accessed by who, when, from which devices and whether those devices are compromised or infected.
Outsourcer devices that are compromised could be a launching pad into your organization and contractor devices that are infected could propagate malware like WannaCry to your internal systems causing financial damage.
Incumbent remote access technologies like VPN and RDP are only exacerbating the problem. They are insecure, slow, hard to deploy and do not meet the usability, security and compliance needs of the leading companies.
It is high time for a paradigm shift!
Fyde eliminates security risks associated with traditional VPN access. Fyde’s innovative approach is driven by identity-aware access control and device-trust based security policies. Our modern VPN alternative enables secure, reliable and fast access to authorized apps and workloads in your network from any device, network, and location.
It’s easy to deploy, monitor and manage, and excels with reliable connectivity and low latency. Stay in charge and maintain full access control to your resources.
Fyde eliminates security risks associated with traditional VPN access. Fyde’s innovative approach is driven by identity-aware access control and device-trust based security policies. Our modern VPN alternative enables secure, reliable and fast access to authorized apps and workloads in your network from any device, network, and location.
It’s easy to deploy, monitor and manage, and excels with reliable connectivity and low latency. Stay in charge and maintain full access control to your resources.


Avoiding a breach through your outsourcing partner
5 min installation • Try all features free for 14 days • No credit card required
5 min installation • Try all features
free for 14 days • No credit card required